CCTV and Access Control Integration: How They Work Together
.png)
Video surveillance and physical access control serve different functions. Cameras record activity, while access control systems validate credentials and govern door states. Each covers a blind spot in the other. A badge reader confirms authorization but cannot verify who walked through.
A camera captures movement but cannot determine whether someone is authorized to be there. When these systems share event data in real time, operators gain a combined view of events as they happen.
The Event-Linking Model
Integration between video software and a physical access control system (PACS) works on a straightforward principle: an event in one system triggers an automated response in the other.
In an integrated deployment, a specific alarm event at a door can automatically activate the associated video equipment and display captured images on designated monitor equipment. The operator sees the alarm and the camera feed simultaneously, without navigating to a separate interface or manually searching for the right camera.
The integration model is not limited to one-way event triggering. Access control events such as a denied credential or a door forced open can pull up associated video feeds. Video-side detections can also be evaluated alongside access events so operators can compare what happened on camera with what appears in the access log.
How the Protocol Stack Connects Them
Integration spans multiple layers of the physical security infrastructure, and each layer has its own communication standard.
Reader to Controller
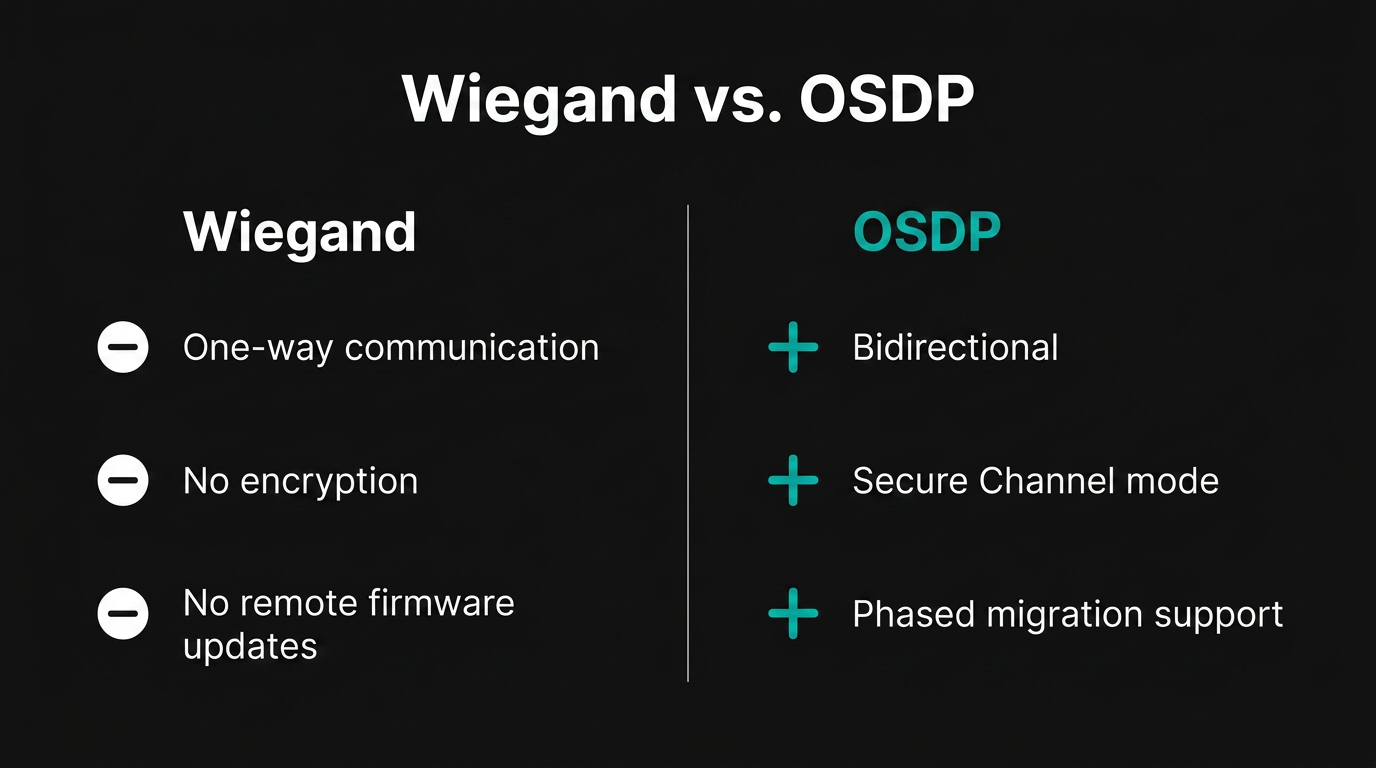
At the field device layer, credential readers communicate with access control panels. The legacy protocol for this connection is Wiegand. Wiegand cannot support bidirectional communication, remote firmware updates, or encrypted credential exchange.
The replacement is OSDP (Open Supervised Device Protocol). OSDP supports Secure Channel mode and enables bidirectional communication between reader and panel. Controllers that support both Wiegand and OSDP connections allow phased migration without full hardware replacement.
Controller to VMS and Management Software
At the IP network layer, ONVIF (Open Network Video Interface Forum) profiles govern how access control systems, cameras, and management software exchange data. ONVIF structures its specifications into profiles, each defining a fixed set of mandatory and conditional functions, with some specifications also identifying optional functions.
Profile A covers access control configuration, including rules, credentials, schedules, and event handling. Other ONVIF profiles address real-time door control, alarm management, video streaming, metadata, and analytics event delivery. Different ONVIF profiles can be supported together depending on the application.
Why This Layering Matters
OSDP and ONVIF operate at distinct layers and serve complementary functions. Organizations that treat integration as a single product decision often introduce gaps at the handoff between layers, because a reader-to-panel protocol problem looks very different from an IP-layer interoperability failure.
Operational Workflows in Practice
The value of integration shows up in repeatable scenarios where credential data and video data need to be evaluated together.
Door Forced Open Verification
A door contact sensor detects an open state with no preceding valid credential read. The PACS generates a Door Forced Open alarm. In an integrated system, the associated camera feed appears at the operator's console automatically. The operator evaluates whether the door was pried open, whether a badge tap failed to register, or whether the door contact sensor is misaligned.
Tailgating Detection
Standard access control validates a credential but does not confirm that only one person transits per authorization. A video-based detection layer counts individuals crossing the threshold per badge event. When the person count exceeds what a single credential authorization permits, the system generates an alert containing both the credential identity and video of the crossing.
The credential-plus-video combination allows security directors to distinguish between piggybacking and tailgating. That distinction can affect incident handling and policy response differently and cannot be made from either data source alone.
Post-Incident Investigation
Without integration, investigators audit the access log, identify timestamps, then separately search video archives for matching footage. With integration, each access log entry links directly to its corresponding video clip. The manual correlation step disappears.
Emergency Mustering
During an unplanned evacuation, the access control system provides the data source for personnel accountability: which credentials were last recorded at which zone entry points. Temporary visitor credentials generate access events in the same system, which can support broader evacuation accountability across employees, visitors, and contractors.
Camera feeds covering assembly areas allow a remote incident commander to visually confirm crowd formation and identify individuals who may be injured or unable to self-report.
After-Hours Access Verification
A credential read at a restricted zone outside normal business hours generates a higher-priority event in most access control configurations. With video integration, the corresponding camera feed accompanies the access event, allowing the operator to confirm the cardholder's identity, observe what they carried in, and verify they left when expected.
The same logic applies to data centers, pharmaceutical storage, and executive floors, where credential validity alone does not establish appropriate intent.
Visitor Management Coordination
Visitor management workflows generate temporary credentials with defined access windows. Linking those credentials to camera feeds at lobby entries, elevator banks, and destination floors creates a verifiable record of the visit.
If a visitor deviates from the expected path or attempts access outside the authorized window, the integrated system captures both the access attempt and the matching video, which supports escort policy enforcement and reduces reliance on paper sign-in audits.
Mapping Cameras to Doors and Events
A working integration depends on accurate associations between physical hardware and digital events. Each door, reader, and alarm point in the access control system needs to be linked to one or more cameras with the appropriate field of view. The relationship is rarely one-to-one. A single secured entry may correlate to an outside approach camera, an interior lobby camera, and a turnstile counting camera, each contributing different information to the same event.
Event mapping defines which access events trigger which video responses. A denied credential read might surface a recorded clip of the attempt, while a door held open alarm might pull the live feed and extend the recording buffer. Without explicit mapping, operators receive either too much noise or miss the connections that integration was meant to provide.
Latency tolerances also shape mapping decisions. A door unlock command that waits for video frame analysis before granting access creates a different user experience than one where the camera correlation happens after the door cycles. Designing the integration around the security purpose of each event, rather than treating all events identically, is part of the work.
Cybersecurity Obligations for Converged Systems
IP cameras, access controllers, and door hardware connected to enterprise networks carry cybersecurity obligations that facilities managers cannot delegate to IT alone.
Physical access control systems and physical environment monitoring systems are classified as operational technology (OT) in NIST SP 800-82 Rev. 3. In converged PACS and video environments, that means OT cybersecurity practices apply to the physical security stack, including network separation between corporate and OT networks, multi-factor authentication for remote access, and role-based access control following the principle of least privilege.
For physical security devices on shared IP infrastructure, segmentation helps limit how far a compromise can spread between enterprise and OT environments. Dedicated VLANs, firewall-enforced boundaries, and controlled access between zones are part of the same discipline when PACS, cameras, and management systems share networked infrastructure.
Defense-in-depth guidance for industrial control and OT environments often emphasizes that security controls must be adapted to operational requirements, including performance constraints. A door unlock command delayed by an additional inspection layer creates a different kind of security problem. Facilities managers need to evaluate security controls against operational latency tolerances, not just cybersecurity effectiveness.
How AI Changes the Operator's Role
The integration model described above relies on rule-based triggers: a door alarm fires, a camera feed appears. AI adds a layer that evaluates patterns across both data streams continuously instead of relying only on a single event trigger.
AI-enabled platforms can compare credential activity with video context to surface events that warrant review, including unusual access activity or threshold crossings that do not match the associated badge event. Real-time correlation of PACS event data with video feeds is a key characteristic of this approach.
Video surveillance is the most commonly integrated technology pairing in the ASIS International Access Control Research Report. With that integrated foundation in place, the operator's role shifts toward reviewing flagged events and making escalation decisions.
AI adds operational value only when the integration is disciplined, the system is tuned over time, and operators have clear boundaries for when to verify, escalate, or override an alert. Organizations that use it to support skilled operators, rather than to replace established security controls or human judgment, reduce the risk of adding complexity without improving response.
Frequently Asked Questions
What are the key differences between Wiegand and OSDP protocols for access control reader-to-controller communication?
Wiegand transmits unencrypted voltage pulses over two wires, making interception straightforward. OSDP uses serial communication with AES-128 encryption in Secure Channel mode, includes tamper detection, and enables controllers to monitor reader health through continuous polling.
How do you accurately map cameras to doors and access points to avoid alert fatigue or missed events in an integrated system?
Start with a physical site survey documenting sightlines and coverage gaps. Assign cameras by security purpose, not proximity. Test event triggers under realistic conditions, refine thresholds iteratively, and involve operators in tuning sessions to validate correlations.
What cybersecurity best practices should be followed when connecting CCTV cameras and access control systems to the same IP network?
Implement firmware updates, disable default credentials, encrypt data in transit using TLS, monitor network traffic for anomalies, maintain asset inventories, conduct vulnerability assessments, deploy intrusion detection systems on physical security VLANs, and establish incident response procedures.

.avif)

