Industrial Access Control: Credentials, Hardware, and Compliance Across Hazardous Facilities
%20(1).png)
Industrial access control governs who enters specific zones within manufacturing plants, refineries, power stations, and other heavy industry sites. Industrial physical access control systems (PACS) operate under distinct constraints, including hazardous atmospheres, PPE constraints, and sector-specific regulatory mandates.
This article examines how industrial PACS differs from commercial building systems and what matters in credential selection, hardware selection, and system evaluation.
Key Takeaways
- Industrial PACS sits within operational technology, governed by zone-based architecture and reliability expectations that diverge sharply from commercial building deployments.
- Credential and hardware selection in hazardous facilities must account for PPE usability, RFID frequency trade-offs, and explosion protection certification under ATEX, IECEx, and the NEC.
- Overlapping mandates from OSHA, NERC CIP, CFATS, MTSA, and NIST SP 800-82r3 create a standards coordination burden that falls entirely on the practitioner.
- Contractor credentialing remains the primary operational vulnerability across every industrial vertical, separating a working access control system from a functioning access control program.
How Industrial PACS Differs from Commercial Building Systems
The most consequential structural distinction is classification. NIST SP 800-82 Revision 3 classifies physical access control systems as a category of operational technology (OT), listing PACS alongside industrial control systems and building automation systems. That classification places industrial PACS within OT-oriented reliability expectations, network segmentation practices, and security control overlays that differ from typical IT-centric commercial deployments.
The consequences of a breach differ as well. Unauthorized entry into an industrial control area can create risks far beyond property loss, including injury, environmental damage, and product contamination. An unauthorized entry into a chemical processing zone carries a fundamentally different risk profile than an unauthorized badge-in at a corporate lobby.
Zone Architecture and the Purdue Model
The Purdue Enterprise Reference Architecture provides a framework for categorizing industrial systems into distinct layers from physical equipment on the factory floor up to enterprise-level information systems.
The zones-and-conduits model assigns each zone a Target Security Level based on threat risk determined by risk assessment. Zone assignments follow a formal security risk assessment process under ISA/IEC 62443-3-2, which applies to industrial automation and control systems.
NIST SP 800-82r3 specifies that unauthorized physical access to OT networks and devices could cause serious disruption and recommends separate authentication mechanisms and credentials for corporate and OT network users. A single badge granting access to both the corporate office and the SCADA control room may not align with this guidance.
Credential Technologies in Industrial Environments
Credential types deployed across industries range from smart RFID cards and proximity cards to keypads, biometric readers, and mobile device credentials. Industrial environments add constraints that narrow this range considerably.
RFID Frequency Trade-offs
Industrial access programs use several RFID credential types. Low-frequency RFID remains common in some environments. High-frequency RFID is often used where organizations want stronger credential features for personnel access. Ultra-high-frequency RFID is well suited to longer-range identification and is often associated with asset tracking rather than personnel authentication.
Communication Protocols
Open Supervised Device Protocol (OSDP) is used when practitioners want supervised communications, reader-controller security features, and device management capabilities beyond those of legacy Wiegand interfaces. For industrial deployments, that matters most where practitioners need supervised communications, stronger reader-controller security, and a protocol that fits broader critical infrastructure security expectations.
Biometric Viability Under PPE
Biometric adoption projections from commercial security research do not transfer to industrial settings without a PPE accommodation analysis.
Fingerprint authentication works only for users not wearing gloves, and face and iris recognition have significant usability issues for workers required to wear respiratory protection or other obstructive PPE. PPE requirements for a given workforce must be considered when selecting biometric authentication methods, as environmental hazards may reduce the effectiveness of biometric methods or preclude them entirely.
In many industrial environments, workers frequently wear gloves, respiratory protection, or other PPE that can limit biometric usability. In practice, these constraints often push industrial PACS designs toward contactless credentials and other methods that remain usable when PPE is required.
Hazardous Area Hardware Requirements
Standard access control readers can ignite flammable atmospheres. In oil refineries, chemical plants, grain silos, and mining operations, electronic equipment installed in classified hazardous areas, including card readers, typically must be approved or certified for the specific hazardous location.
ATEX applies under Directive 2014/34/EU. In the United States, hazardous-location electrical requirements are addressed by NFPA 70 (the NEC) and enforced through applicable regulations such as OSHA requirements. IECEx applies internationally under the IEC 60079 series.
Explosion-proof enclosures contain an internal explosion without igniting the surrounding environment. Intrinsically safe designs limit energy through IS barriers to prevent ignition entirely. In the highest-risk environments, only certain protection methods are permitted, while less restrictive classified areas permit a broader set of protection methods.
ATEX and IECEx certification falls outside both ISA/IEC 62443 and NIST SP 800-82. Practitioners must address it through the applicable directives as a separate design and procurement requirement, or risk overlooking it entirely.
Regulatory Frameworks Governing Industrial Access Control
Physical access control at U.S. industrial facilities falls under overlapping federal mandates, each with distinct sector applicability and enforcement mechanisms.
OSHA and the General Duty Clause
Section 5(a)(1) of the Occupational Safety and Health Act requires employers to furnish a workplace free from recognized hazards likely to cause death or serious physical harm. Specific standards with direct physical access control obligations include requirements to prevent unauthorized entry to permit-required confined spaces. OSHA enforcement actions also show how access failures can become entangled with lockout/tagout and machine guarding violations.
NERC CIP-006 for Electric Utilities
NERC CIP-006 is one of the most prescriptive physical access control regimes in U.S. industry. It requires a Physical Security Plan with electronic access control at each Physical Security Perimeter, a visitor control program with continuous escorted access, and testing of locally mounted hardware including badge readers and electronic lock mechanisms. CIP-006-7, subject to future enforcement, adds a requirement to issue an alarm within 15 minutes of detected unauthorized access. Physical security requirements under CIP-006 remain an important area of NERC CIP compliance focus.
CFATS for Chemical Facilities
High-risk chemical facilities possessing chemicals of interest fall under the Chemical Facility Anti-Terrorism Standards. Facilities must develop security plans meeting Risk-Based Performance Standards, including access screening and personnel surety. Practitioners should verify CFATS program status directly with CISA, as statutory authorities have lapsed and CISA cannot currently require facilities to submit information in CSAT.
MTSA for Maritime Port Facilities
Facility Security Plans with access control as a primary measure are mandatory under the Maritime Transportation Security Act. Workers who need unescorted access to secure areas of MTSA-regulated facilities must hold a Transportation Worker Identification Card, while others may be escorted or fall under specific exemptions.
NIST SP 800-82r3 and SP 800-53r5
NIST SP 800-82 Rev. 3 includes an OT overlay to SP 800-53 Rev. 5, with tailored security control baselines. The PE control family includes physical access authorizations and physical access control requirements, including enhancements such as continuous guards. These are mandatory for federal agencies and widely adopted as a voluntary baseline in the private sector.
Integration with Industrial Safety Systems
Lockout/Tagout Authorization
OSHA states that authorized employees use personal lockout/tagout devices and that energy cannot be restored until all employees have removed their personal devices. That individual accountability requirement may help explain the use of badge-based LOTO authorization in PACS-integrated systems, but OSHA does not explicitly identify it as a direct regulatory driver for those systems. Electronic LOTO integrated with PACS remains an emerging approach, and practitioners must verify that any electronic system fully satisfies OSHA 1910.147's requirements before deployment.
Emergency Mustering
Badge transaction records that control zone access generate the last-known-location data mustering systems query during an emergency to determine who is on-site, in which zone, and whether they have reached a designated muster point. NIST SP 800-82r3 includes PACS within its OT scope and discusses supporting emergency operation through graceful degradation, but it does not explicitly extend that guidance to mustering. The system must function in a degraded or offline state if the primary PACS network fails during an emergency.
SCADA and ICS Network Segmentation
NIST SP 800-82r3 recommends restricting both logical access to OT networks and physical access to OT networks and devices. Physical PACS controls therefore operate as one layer in a broader defense-in-depth architecture rather than as a standalone boundary.
Vertical-Specific Deployment Considerations
Power Generation and Utilities
NERC CIP-014 requires physical security plans that collectively deter, detect, delay, assess, communicate, and respond to potential threats. Remote, unmanned substations present a particular challenge, requiring cameras, fencing, and detection systems where permanent staffing is not viable.
Oil, Gas, and Chemical Processing
In U.S. oil and gas hazardous environments, electrical hardware selection is generally based on NEC hazardous location classifications. Class I locations dominate these facilities. The most hazardous locations require explosion-proof or intrinsically safe equipment. Periodic planned maintenance shutdowns create a contractor credentialing surge where populations may increase dramatically, straining standard visitor management workflows.
Manufacturing
NIST SP 800-82r3 classifies manufacturing PACS as operational technology subject to OT security control baselines, including physical access authorization and tamper protection requirements. Equipment must withstand corrosive conditions characterized by high temperature, humidity, and chemical exposure.
Water Treatment
America's Water Infrastructure Act of 2018 requires community water systems serving more than 3,300 people to complete a Risk and Resilience Assessment and Emergency Response Plan on a recurring cycle. The EPA requires these assessments to cover physical barriers and facility security. A single water utility may operate distributed pump stations, reservoirs, and monitoring points, many unstaffed, all requiring access control coverage.
Mining
Underground mining operations may require intrinsically safe or dust-ignition-protected equipment depending on the environment. The NEC defines hazardous locations for combustible dust, but coal mines are regulated under separate mining safety requirements rather than being specifically described online as facing NEC Class II requirements.
Remote and distributed entry points across large concession areas present credentialing and monitoring challenges similar to water utility pump stations. Underground mining's access control requirements intersect directly with mustering and personnel tracking obligations, extending well beyond the entry/exit model used in surface facilities.
Technology Trends and Trade-offs
Mobile Credentials
In shop-floor or field operations roles without company-issued devices, the model's value degrades. Practitioners deploying mobile credentials in petrochemical or mining environments must independently verify RF compliance.
Cloud-Managed Access Control
Safety-critical door controllers must retain local credential caching and local decision-making capability. Administrators use cloud infrastructure for policy propagation and audit log aggregation, but it cannot serve as the sole authentication point for doors where an outage would create a safety hazard.
IT/OT Convergence
Unified identity platforms using a single credential set for both IT and OT access may be difficult to reconcile with NIST SP 800-82r3. Access control systems must maintain local intelligence independent of the converged IT network at safety-critical access points.
Evaluation Criteria for Industrial PACS
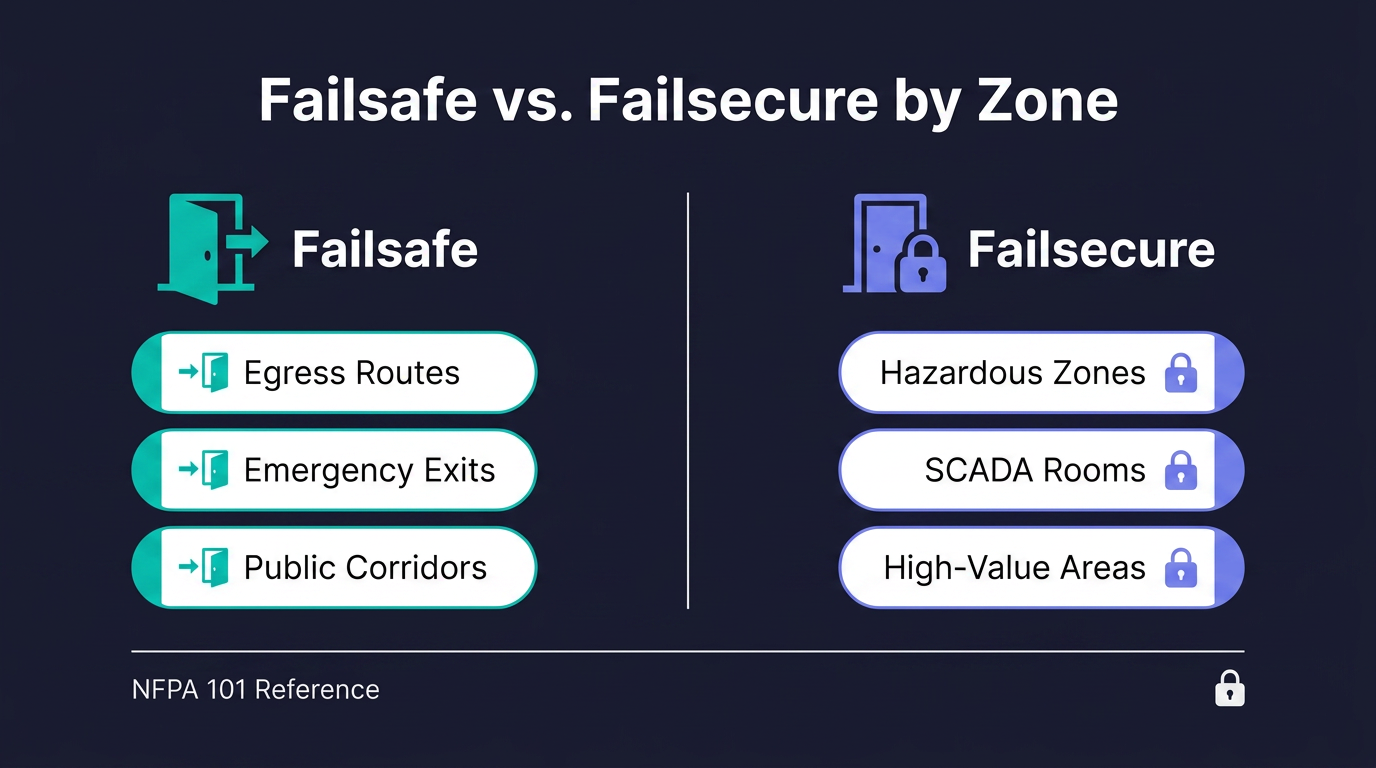
Failsafe Versus Failsecure by Zone
Doors serving high-value or hazardous areas should be failsecure while meeting egress requirements. NFPA 101 requires doors in the means of egress to be operable from the egress side without keys, tools, or special knowledge, with limited exceptions for approved delayed-egress and access-controlled locking arrangements that must release under specified conditions. NIST SP 800-82r3 provides general guidance on OT security, including access control and safety considerations. Authorities Having Jurisdiction, including fire marshals and building code officials, must be consulted before finalizing any selection.
Backup Power
Industrial PACS deployments need backup power for readers, controllers, and related devices where an outage would disrupt security or safety functions. Generator-backed power and communications redundancy may also be relevant where facilities need continued operation through extended outages.
Hardware Durability
Industrial environments place unusual stress on access control hardware and supporting power infrastructure. Electrical noise, transient conditions, temperature, humidity, and chemical exposure all affect equipment selection and installation quality.
Contractor Access Management
Across every industrial vertical, contractor access represents the primary operational vulnerability. The credentialing spectrum ranges from a vendor coming for a brief visit, to regular contractors on-site multiple times per week, to a repair contractor on-site for several days, to a long-term contractor filling in for weeks. Each scenario requires different credential duration, access scope, escort requirements, and audit trail depth.
Credentials that are too broad, too long-lasting, or not properly revoked represent the gap between having an access control system and having an access control program.
The Standards Coordination Problem
No single framework covers the three domains that converge at every industrial access point: cybersecurity (ISA/IEC 62443), physical safety (OSHA 29 CFR 1910), and explosion protection (ATEX/IECEx/NEC). Each is maintained by a separate body, updated on a separate cycle, and audited by separate authorities. That coordination burden falls entirely on the practitioner. Facilities may encounter NIST SP 800-82r3's OT requirements through procurement and system upgrade decisions, but implementation timing will vary by organization.
Frequently Asked Questions about Industrial Access Control
Who Should Own Industrial PACS Within an Organization?
Ownership typically spans facilities, corporate security, and OT engineering, with compliance functions sharing accountability in regulated sectors. A documented responsibility matrix covering credentialing, hardware lifecycle, and audit response prevents the gaps that surface during regulatory inspections and incident reviews.
What Documentation Should Industrial PACS Maintain for Regulatory Inspections?
Inspectors expect access authorization records, credential issuance and revocation logs, hardware test results, visitor and contractor escort records, and evidence of perimeter integrity. Retention requirements vary by framework, so document control procedures should align with the most stringent applicable obligation.
How Should Industrial Sites Respond to a Confirmed Unauthorized Access Event?
Response begins with isolating the affected zone, verifying personnel safety, and preserving badge transaction logs and video evidence for investigation. Notification obligations under sector regulations follow, alongside root cause analysis covering credentialing, escort procedures, and hardware integrity.

.avif)

