RFID Access Control: How it Works, Frequencies, and Use Cases

Radio-frequency identification (RFID) access control uses contactless credentials to unlock a door when presented near a reader. Similar-looking credentials can operate through different frequency bands, electromagnetic mechanisms, and security models. Those differences affect read range, authentication options, and deployment risk. In physical access control, the choice of credential shapes both day-to-day operation and the security weaknesses a system must address.
How RFID Credentials Communicate with Readers
A physical access control system (PACS) uses electronic authentication at access points to control entry to protected areas. In RFID implementations, a credential (card or fob) communicates with a reader through one of two electromagnetic mechanisms. The mechanism in use determines read range, power requirements, and security posture.
Inductive Coupling for LF and HF Credentials
Low-frequency (125 kHz) and high-frequency (13.56 MHz) credentials use inductive coupling. The reader's antenna coil generates an oscillating magnetic field. When a credential enters that field, its own antenna coil acts as the secondary winding of a transformer, and the reader's field induces enough voltage to power the credential's circuitry without a battery. Passive LF and HF tags are inductively coupled and do not communicate via backscatter.
HF credentials at 13.56 MHz operate at short ranges, typically requiring close presentation in standard access control applications. This short range is an operational security feature: it requires deliberate, proximate presentation of the credential, reducing exposure to unauthorized standoff reads.
Backscatter for UHF Credentials
Ultra-high-frequency (860–960 MHz) credentials operate through a different physical mechanism called backscatter. The tag's antenna captures radiated energy from the reader's transmission and communicates back by modulating the reflection of the incoming signal. At the hardware level, passive UHF RFID tags are generally described as including an antenna and an integrated chip or rectifier circuitry for power harvesting and backscatter communication, with data encoded by changing the tag's impedance and thus its reflectivity to the reader.
This arrangement creates a security-relevant asymmetry: the reader's forward-channel signal is much more powerful than the tag's back-channel response. An attacker can detect that a reader is active from a greater distance than they can intercept the tag's reply. This has direct implications for eavesdropping risk.
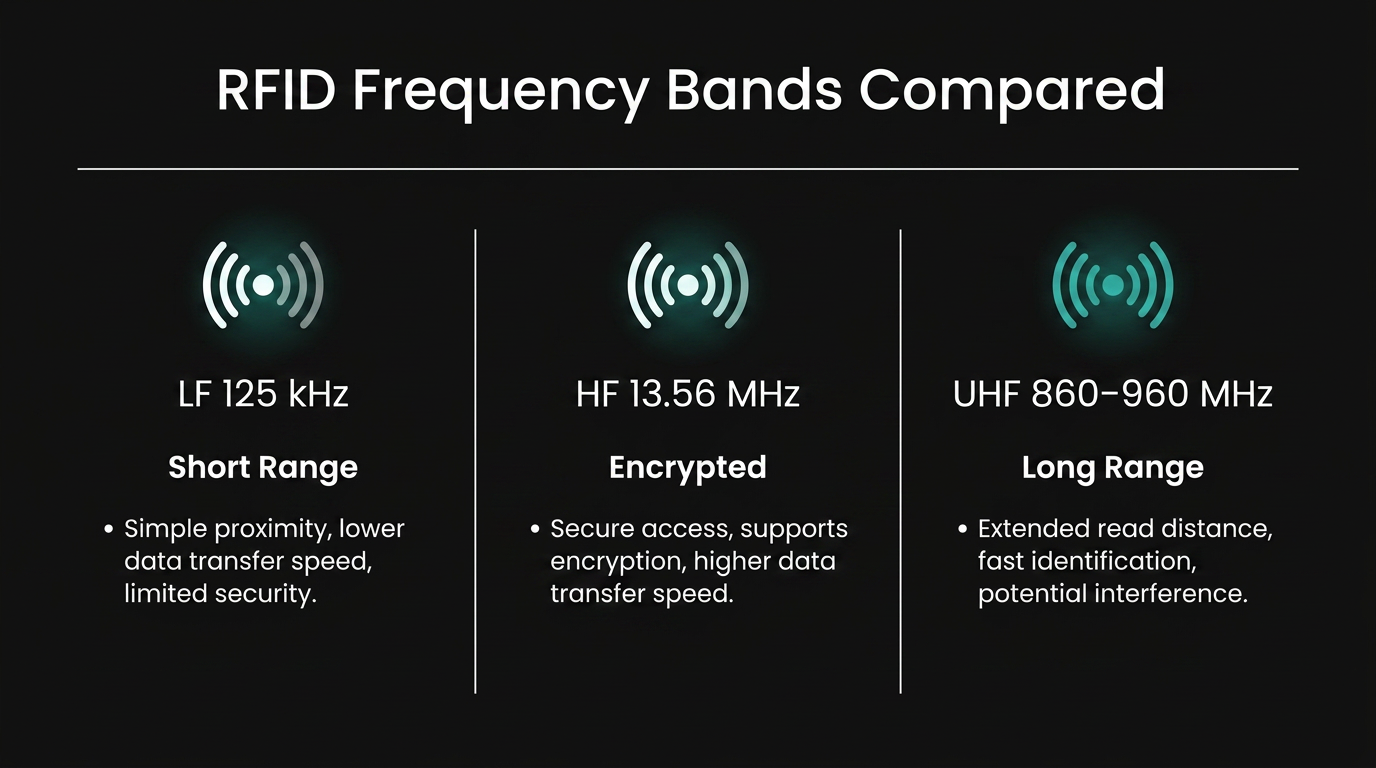
Three Frequency Bands Compared
Low-Frequency Credentials at 125 kHz
LF credentials are commonly described in legacy proximity deployments as unencrypted and exposed to duplication, and the absence of authentication means the reader checks only a static identifier value rather than verifying the credential itself. 125 kHz proximity technology is commonly described as a passive RFID system in which the reader emits a short-range RF field that powers the credential, which then transmits its identifier back to the reader.
LF performs well near metals and liquids compared with higher RFID bands, which made it useful in environments where nearby materials could be unpredictable. But the absence of any authentication mechanism means a reader cannot verify that a presented credential is genuine. It checks only the static identifier value.
High-Frequency Credentials at 13.56 MHz
HF credentials at 13.56 MHz support substantially greater data capacity and, at the application layer, AES-128 encryption with mutual authentication. Two primary ISO standards govern the RF interface:
- ISO/IEC 14443 defines proximity coupling with a communication range typically described as very short. It is the basis for U.S. federal PIV cards and DoD Common Access Cards.
- ISO/IEC 15693 defines vicinity coupling for contactless cards, which is commonly described as supporting longer read ranges depending on the reader, tag, and environment.
The base ISO standards do not themselves mandate encryption. Cryptographic security, including AES-128 and mutual authentication found in implementations such as MIFARE DESFire EV2/EV3, operates at the application layer above the base standard. 13.56 MHz contactless smart cards are widely used for access control and are associated with ISO/IEC 14443 and ISO/IEC 15693 technologies.
NFC-based mobile credentials also operate at 13.56 MHz, placing smartphone credentials within the same HF standards framework.
Ultra-High-Frequency Credentials in the 860–960 MHz Band
UHF credentials offer longer read ranges for passive tags and support simultaneous reading of multiple tags at high speed. These properties make UHF relevant to vehicle access and parking scenarios.
The base EPC Gen2 standard (ISO/IEC 18000-6C) does not include the same kind of cryptographic authentication available in many ISO/IEC 14443 application-layer implementations. ISO documentation standardizes UHF RFID in the 840–960 MHz range, while industry sources commonly associate this band with logistics and supply-chain applications.
UHF is also not globally harmonized: the United States allocates 902–928 MHz while Europe uses 865.6–867.6 MHz. Organizations operating across multiple countries must account for this fragmentation. UHF systems additionally operate in shared ISM bands and face interference from SCADA, industrial automation, building automation, and consumer devices.
Security Vulnerabilities Across Credential Types
The 125 kHz Cloning Problem
The vulnerability of 125 kHz credentials is architectural. Legacy access-control systems commonly use Wiegand-formatted data between readers and controllers. One-way, unencrypted, with no mechanism for the reader to verify credential authenticity. Low-cost cloning tools are widely available. Security planning for these systems generally points toward modernization rather than incremental mitigation.
Credentials using proprietary security designs also present migration risk. MIFARE Classic credentials operate at 13.56 MHz and use the proprietary CRYPTO1 cipher. Organizations still deploying them should treat those credentials as higher-risk for assessment and migration planning.
Active CVEs on Deployed Platforms
A CISA advisory on HID Global iCLASS SE and OMNIKEY products describes an Improper Authorization vulnerability affecting all versions of HID iCLASS SE CP1000 Encoders, iCLASS SE Readers, iCLASS SE Reader Modules, iCLASS SE Processors, and multiple OMNIKEY reader models when configured as encoders. Certain communication channel configurations could expose sensitive data when reader configuration cards are programmed, including credential and device administration keys.
Physical security directors should apply the same patch management and firmware update discipline to RFID readers and controllers that they apply to other connected infrastructure.
The Reader-to-Controller Protocol Gap
Even a cryptographically strong credential can be undermined by the protocol carrying data from reader to controller. Wiegand, still deployed across millions of doors, transmits credential data unencrypted in one direction. A DESFire EV3 card authenticating over AES-128 loses its security advantage if the data path between reader and panel is unprotected.
SIA's Open Supervised Device Protocol (OSDP), published as international standard IEC 60839-11-5, addresses this gap. OSDP v2 supports bi-directional communication, AES-128 encryption via SecureChannel, and line supervision with tamper detection.
RFID Access Control Use Cases by Vertical
Federal Facilities
Federal facilities operate under the most prescriptive credential standard of any vertical. The governing credential is the PIV card, a contactless smart card carrying PKI certificates and biometric data. Federal procurement for PIV-related PACS relies on the GSA Approved Products List as a compliance pathway.
PACS deployed in many federal buildings remain facility-centric rather than enterprise-centric, using proprietary architectures that limit interoperability across agencies.
Healthcare
Healthcare facilities often use separate systems for access control and for tracking people or assets in motion. Staff commonly carry 13.56 MHz HF smart cards for access control to restricted areas such as medication rooms, ICUs, and operating suites. Healthcare organizations should evaluate access-log handling alongside HIPAA privacy and security obligations when those logs are tied to restricted clinical areas.
Education Campuses
Campus card programs often use a single physical credential for access control, cashless payment, library systems, and dining. The higher data capacity of 13.56 MHz HF credentials supports this multi-application architecture. A 125 kHz proximity card is generally used for access-only applications, which can push campuses toward parallel credential systems with associated management overhead.
UHF is deployed separately for parking access, where long read ranges are operationally necessary. Cards following ISO 14443 and ISO 15693 standards can support compatibility across reader manufacturers from different procurement cycles.
Manufacturing Plants
Manufacturing often requires a multi-frequency RFID deployment environment. LF at 125 kHz remains common for door and gate access because it performs well near metal, a decisive property where HF credentials degrade near metal door frames and structural elements.
RFID tags can track work-in-progress across production floors, while active RFID systems are also used for real-time location tracking of assets and personnel in some manufacturing environments. Compliance and operational planning in these environments often include emergency mustering, controlled-area access logging, and documented physical access controls.
Commercial Buildings
Commercial buildings often contain more than one credential generation at the same time rather than a clean technology choice. Legacy 125 kHz proximity cards remain deployed alongside newer 13.56 MHz smart cards and an emerging layer of NFC and BLE mobile credentials. Multi-tenant properties often need distinct credential policies for employees, contractors, and visitors. In those environments, segmentation, provisioning discipline, and tenant-specific access boundaries all affect the security impact of a credential system failure.
Where RFID Fits Among Other Credential Technologies
RFID credentials represent one authentication factor: something you have. NIST SP 800-63B classifies PINs as something you know and biometrics as something you are, and it explicitly prohibits standalone biometric authentication. Biometrics must pair with a physical authenticator. This has direct procurement implications: biometric readers should always be specified as part of a two-factor configuration, not as replacements for card readers.
BLE mobile credentials share the "something you have" classification with RFID cards and can support hands-free access scenarios. That extended range can increase exposure to relay-style attacks if distance-bounding mechanisms are not in place. NFC mobile credentials, by contrast, operate at the same 13.56 MHz frequency as HF smart cards and are typically optimized for very short distances.
Frequently Asked Questions
What are the key differences between Wiegand and OSDP protocols for reader-to-controller communication in access control systems?
Wiegand lacks encryption and transmits one-way, making it vulnerable to interception and replay attacks. OSDP uses bidirectional communication with AES-128 encryption, line supervision, and tamper detection, enabling secure credential transport and real-time integrity monitoring between readers and panels.
How do you migrate from legacy 125 kHz proximity cards to 13.56 MHz smart cards without disrupting building operations?
Deploy dual-frequency readers that accept both credential types simultaneously, issue new credentials in waves by department or zone, run both systems in parallel during transition, then decommission legacy cards after verifying full migration and testing failover scenarios.
Why does NIST prohibit standalone biometric authentication, and how should biometric readers be configured in a physical access control system?
NIST prohibits standalone biometric authentication because biometric data can be copied or spoofed and cannot be revoked once compromised. Biometric readers must pair with a physical authenticator like a card to create two-factor authentication.

.avif)

