Touchless Access Control: How Contactless Entry Works

Touchless access control authenticates a user without physical contact with the reader. Instead of swiping a card or entering a PIN, the credential exchange occurs via a wireless protocol, biometric capture at a distance, or both.
The underlying access control logic remains the same. Security teams evaluating touchless systems need to compare credential technologies, security risks, and compliance requirements before specifying or upgrading a deployment.
Key Takeaways
- Touchless access control spans NFC, BLE, UWB, and biometric modalities, each offering distinct tradeoffs between range, convenience, and relay attack exposure.
- Biometric deployments carry permanent consequences because compromised identifiers cannot be reissued, making template storage architecture a foundational design decision.
- Compliance obligations vary significantly across jurisdictions, requiring multi-site organizations to map every facility location against applicable biometric privacy laws before enrollment.
- Credential systems do not prevent tailgating on their own, so layered controls such as occupancy sensing, optical turnstiles, and mantraps remain essential for secure zones.
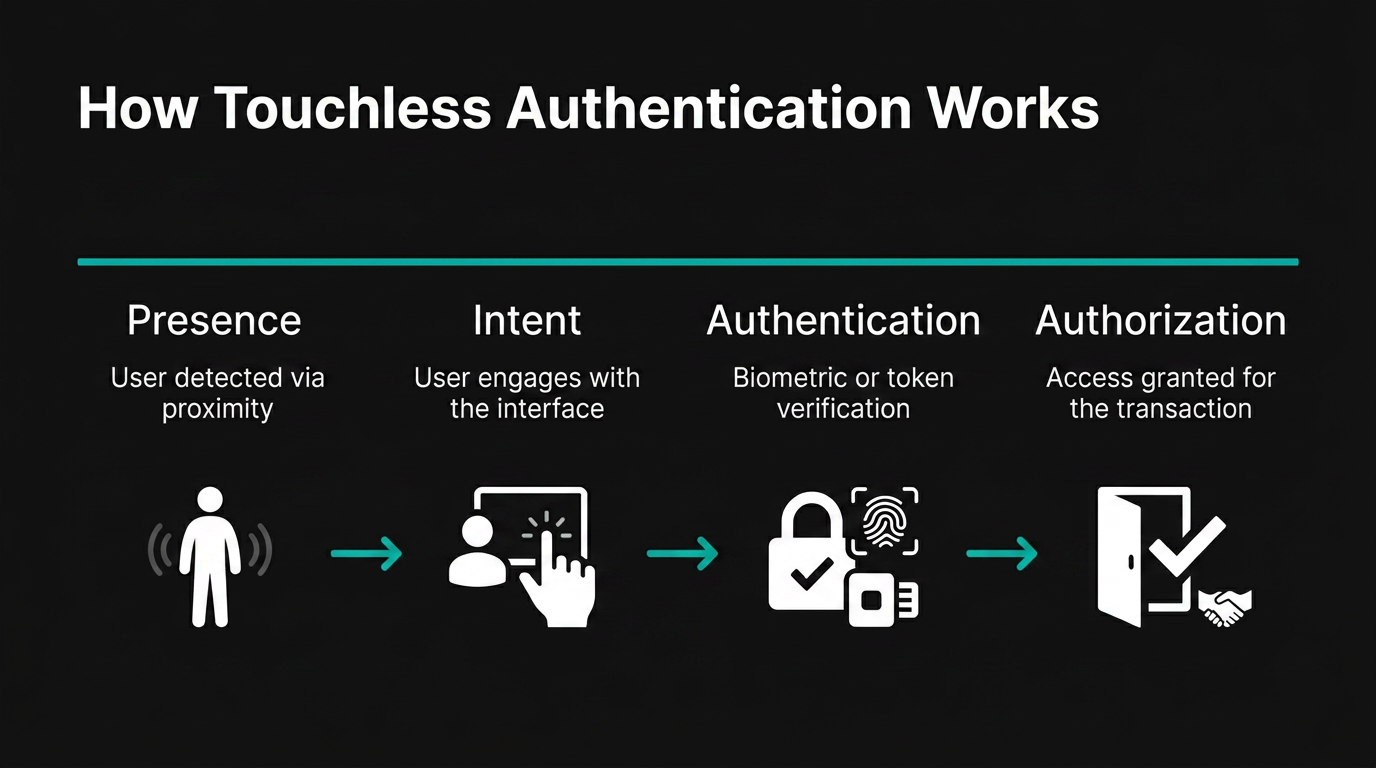
How Touchless Authentication Works
Every touchless access control transaction follows the same sequence, regardless of which credential technology is in use:
- Proof of presence. A user approaches the door, and the reader detects their presence.
- Intent. The system determines the user intends to enter rather than walking past.
- Authentication. The reader validates the credential through a cryptographic challenge-response or biometric template match, communicating with the access controller over OSDP (Open Supervised Device Protocol), developed by SIA.
- Authorization. The access controller queries its rules database to determine whether that credential is authorized for that door at that time. If authorized, the controller signals the door hardware to release.
The critical design variable is where each stage executes. Most touchless credential readers perform cryptographic authentication locally and pass only an authenticated signal downstream to the controller.
Credential Technologies Behind Contactless Entry
NFC (Near Field Communication)
NFC operates over a short range. The reader's RF field inductively powers the credential chip, which responds with an anti-collision sequence and then executes cryptographic authentication. That short range requires a deliberate tap or hold, which limits relay attack surface.
NFC can support compatibility with a range of devices and legacy systems during access control transitions. NFC readers can often read both legacy smart cards and NFC-enabled phones. Adding BLE (Bluetooth Low Energy) capability to the same reader requires a hardware change.
BLE Mobile Credentials
A BLE reader broadcasts advertising packets with a configurable range. When a phone running the credential app enters the configured range, it initiates a BLE connection, and mutual cryptographic authentication occurs.
Tap mode mimics the NFC interaction. Twist-and-go keeps the phone in the user's pocket, with proximity triggering the unlock. Long-range hands-free mode opens the door as the user approaches. Each mode trades convenience against the risk of unintended unlocks, and the configurable range is the primary mitigation.
UWB (Ultra-Wideband)
The distinguishing security property of UWB is precise Time-of-Flight distance measurement using UWB PHY/MAC enhancements operating in UWB bands. Secure ranging, as specified by the FiRa Consortium, measures the relative position of a transmitter and receiver while protecting against attacks.
In a typical UWB access flow, the reader continuously broadcasts ranging signals. When a user's trajectory and proximity confirm intentional approach, the system triggers authentication. UWB is commonly used for ranging and presence detection, with NFC or BLE often handling the cryptographic credential exchange. The result is a hands-free experience where the door opens as a person approaches and locks as they move away.
Biometric Modalities
Biometric capture at distance removes the last physical touchpoint from the authentication sequence.
Facial geometry matching captures an image as a user approaches, extracts facial geometry, and compares the result against enrolled templates. Local processing can keep the biometric template off the network by performing the match at the edge and passing only an authenticated signal to the controller.
Iris scanning uses infrared cameras for close-range capture.
Contactless fingerprint capture allows a user to wave a hand past a reader rather than pressing a finger onto a surface. Some systems simultaneously capture finger vein patterns for multi-factor biometric fusion on a single device.
Wave-to-Unlock
Wave-to-unlock uses infrared or capacitive sensors to detect a hand gesture near the door. The architectural distinction is important: this is a door release mechanism rather than an authentication mechanism. It does not verify identity. In PACS architecture, wave sensors typically serve two roles: post-authentication door release and public-side touchless egress.
System Architecture from Edge to Cloud
A touchless PACS deployment connects credential hardware at the door to centralized decision-making and management software.
The edge layer houses the credential readers, biometric capture devices, optical turnstiles, REX sensors, and door contacts. IP reader-controllers at this layer can connect to existing IT networks via a single PoE cable, reducing installation complexity. OSDP connects readers to the controller layer.
The controller layer makes access decisions. Traditional panels can support a wide range of door counts. Controllers maintain local decision-making during network outages and log events. They receive authenticated credential tokens from readers and evaluate them against access rules.
The software layer includes the PACS management platform (cloud-hosted or on-premise), identity and credential management, visitor management, VMS integration, and API connections to HR and building management systems.
Cloud Versus On-Premise Credential Management
Cloud-managed platforms deliver centralized multi-site administration and automatic updates. On-premise deployments offer greater data sovereignty, lower bandwidth dependency, and direct organizational control. Security outcomes depend on configuration and operations rather than deployment model alone.
Guidelines for the use of PIV credentials in facility access and for integrating them with physical access control systems apply here. Information systems security protections, including network segmentation, patching, and access logging, apply to access control infrastructure regardless of deployment model.
Operational Advantages of Touchless Systems
Reduced surface contact. Keypads for PIN entry are multi-touch surfaces. Touchless biometric access removes those touchpoints, reducing surface contact in high-traffic entries.
Credential integrity. Physical cards can be lost, stolen, or cloned. A cloned credential allows an attacker to move through entry points while appearing to operate under a legitimate user's identity. Deploying mobile credentials and biometrics reduces these risks. Biometric traits cannot be handed to another person.
Audit trail completeness. When physical credentials are shared, the unique-user identification that audit logs depend on breaks down. A touchless biometric system binds each access event to a specific individual rather than a transferable token. Access control data from these systems supports compliance auditing, incident investigation, and operational analytics.
Remote provisioning and revocation. Administrators can grant or revoke mobile credentials instantly, without physical card retrieval or replacement cycles.
Security Risks and Vulnerabilities
Relay Attacks on BLE and NFC Credentials
Relay attacks intercept and forward wireless authentication signals between a legitimate credential and a reader without breaking the cryptographic layer. The attack exploits the physical radio layer.
NFC relay attacks are sufficiently mature to warrant dedicated countermeasures.
Biometric Presentation Attacks
A Presentation Attack Instrument is a biometric characteristic or object used in a biometric presentation attack. Attack types include printed photographs, video replay on screens, and masks cast from artificial materials. Video injection attacks bypass the physical camera entirely by feeding synthetic video directly into the authentication pipeline. Presentation Attack Detection (PAD) systems trained on one dataset may degrade against novel attack instruments absent from their training data.
Biometric Error Rates and Demographic Differentials
False negative error rates in biometric identification vary significantly across algorithms and demographic groups. False negative rates are elevated by inadequate lighting, under-exposure of dark-skinned individuals, and camera positioning that causes pitch-angle variation. These documented differentials create EEOC disparate impact exposure when biometric identification is used for workplace access control.
Biometric Data Irreversibility
Unlike passwords or access cards, compromised biometric identifiers cannot be reissued. A breach creates permanent identity exposure for every affected individual. Technical frameworks for cancelable biometric templates exist, but adoption requires deliberate architectural decisions at the design stage.
Mobile Credential Dependencies
The tradeoff is a different set of failure modes: dead batteries cause access denial, OS updates can break credential applications, and a compromised mobile device can become an NFC relay proxy. Organizations relying on mobile credentials need fallback access methods and defined remote revocation procedures.
Environmental and Operational Factors
Ambient light, direct sunlight, and extreme temperatures degrade the performance of optical biometric readers and infrared sensors. BLE and UWB signal propagation varies with door materials, corridor geometry, and RF interference from adjacent equipment. Site surveys that test reader performance under worst-case environmental conditions prevent post-installation reliability failures.
Regulatory and Compliance Requirements
Biometric touchless access control triggers obligations under a growing and fragmented set of laws. No single federal U.S. biometric privacy statute exists.
U.S. State Biometric Privacy Laws
SIA's Guide to U.S. Biometric Privacy Laws covers states and localities with biometric privacy laws or related requirements.
Illinois BIPA requires written notice, informed consent before collection, a publicly available retention policy, and grants a private right of action with statutory damages per violation.
Texas CUBI imposes requirements on biometric collection and use under state law.
International and Federal Requirements
GDPR classifies biometric data processed for identification as special category data, prohibited by default. Controllers must satisfy the required legal bases and conditions for processing. A DPIA is generally required before deployment where the biometric processing is likely to result in a high risk to individuals' rights and freedoms, including uses for unique identification such as biometric identification for access control.
EEOC guidance explicitly identifies biometric identification that is less accurate for darker skin tones as an example of how AI may violate employment discrimination laws.
ADA accessibility requirements can apply to biometric access points in covered public accommodations and commercial facilities, but not necessarily to every biometric access point.
Multi-Factor Authentication in Touchless Deployments
A core constraint governs touchless biometric deployment: biometrics may be used as part of multi-factor authentication with a physical authenticator.
Touchless MFA Combinations
Touchless enterprise MFA often combines mobile credentials with biometric verification such as facial matching with presentation attack detection (PAD). The mobile device serves as the physical authenticator. Facial geometry matching with PAD tested per relevant standards, using Impostor Attack Presentation Accept Rate and Impostor Attack Presentation Match Rate as evaluation metrics, provides the biometric factor. The biometric template is bound to the mobile credential, which is cryptographically bound to device hardware via a secure enclave.
Contactless PIV smart cards with On-Card Comparison (OCC) can use biometrics instead of a PIN for card activation. An optional on-card biometric comparison mechanism can be used for PIV cards. The contactless interface carries only the result of the cryptographic operation, never the biometric data. This architecture eliminates the template transmission attack surface by design.
Guidance for PACS risk tiers provides the risk-based framework for tiering these combinations across physical zones: Controlled, Limited, and Exclusion areas. Lower-risk lobbies may use lower-assurance access methods based on a risk assessment. Server rooms and exclusion zones may require higher assurance using hardware-based cryptographic authenticators and, in some cases, a biometric factor bound to the authenticator.
Anti-Tailgating as a Separate Control Layer
No credential system, touchless or traditional, inherently prevents tailgating. Credential systems validate credentials, not the number of people passing through a doorway. Requirements for secure areas call for appropriate entry controls and a layered approach so that failure of one mechanism does not result in unrestricted access.
The integration pattern connects camera-based occupancy sensors to the physical access control system. A credential unlock event sets the expected occupancy count. Person detection and line-crossing analysis track individuals crossing the threshold. Any count exceeding the expected value triggers a tailgating event and automated response. For exclusion zones, mantraps provide a physical guarantee: the second door cannot open until the first is confirmed closed and only one person is confirmed present.
Evaluation Considerations for Security Teams
OSDP Verified certification should be strongly considered for new reader hardware.
Biometric template storage architecture is a risk decision with permanent consequences. On-Card Comparison eliminates the template transmission attack surface. Organizations that centralize biometric templates should understand the regulatory exposure that can accompany centralized biometric databases.
Multi-site organizations need to map every facility location against applicable state biometric privacy laws before enrollment begins.
A phased evaluation that maps credential technology against compliance obligations and existing infrastructure will surface integration gaps before they become deployment failures. PACS alarm management capabilities should be evaluated alongside credential technology choices. Organizations can reduce badge reader alerts through intelligent filtering and risk-based prioritization, particularly in corporate campus environments where high volumes of legitimate access events can overwhelm security teams.
Contextual awareness and security and privacy by design principles should guide architecture decisions from the earliest planning stages.
Frequently Asked Questions about Touchless Access Control
How does touchless access control handle visitors and temporary users?
Visitor management platforms can issue mobile credentials or QR codes that integrate with the same readers used for permanent staff. Pre-registration allows credentials to activate on arrival and expire automatically when the visit window closes.
Can touchless and traditional credentials coexist during a phased migration?
Multi-technology readers accept legacy proximity cards, smart cards, and mobile credentials at the same hardware. Phased rollouts let organizations enroll users on the new credential type while maintaining existing badges, then retire legacy cards once enrollment completes across the population.
How does touchless access control integrate with video surveillance?
Access events link to video clips through API connections between the PACS and the VMS, allowing investigators to retrieve corresponding footage for any credential read. Synchronized timestamps enable cross-referencing during incident review and forensic reconstruction of access sequences.
What does enrollment look like for biometric touchless access?
Enrollment captures the biometric trait under controlled conditions and links it to an identity record in the credential management system. Self-service kiosks and remote enrollment via mobile devices reduce the administrative burden of onboarding large populations.